Jim Babka and Downsize DC are a valuable asset, I look forward to the information I receive in the DownsizerDispatch. Today, I received an “URGENT” message stating:
A huge part of the business of politics involves conferring subsidies and special protections on favored companies and industries, making many of them near (or actual) monopolies that also happen to be “too big to fail.” Now here comes the latest example of monopoly creation by The State . . .
The Feds want to monopolize the user names and passwords that you employ on the Internet!
The so-called Department of Homeland Security, in cooperation with major corporations like Microsoft, has drafted what they call a “National Strategy for Trusted Identities in Cyberspace.”
That sounds ominous, and it is. Will you be a “trusted entity,” or a distrusted one?
Of course, the Federal Statists claim that this “strategy” is for your own good. It’s supposed to protect you from identity theft, but it also exempts companies like Microsoft from the burden of creating safe products, while laying yet another brick in the wall of an embryonic police state.
The 39 page National Strategy for Trusted Identities in Cyberspace Draft Proposal states:
“The Strategy’s vision is:
Individuals and organizations utilize secure, efficient, easy-to-use, and interoperable identity solutions to access online services in a manner that promotes confidence, privacy, choice, and innovation.”
“With the vision of the Identity Ecosystem in mind, the National Strategy for Trusted Identities in Cyberspace (NSTIC) identifies the following goals:
Goal 1: Develop a comprehensive Identity Ecosystem Framework
Goal 2: Build and implement an interoperable identity infrastructure aligned with the Identity Ecosystem Framework
Goal 3: Enhance confidence and willingness to participate in the Identity Ecosystem
Goal 4: Ensure the long-term success of the Identity EcosystemThe first two goals focus on designing and building the necessary governance, policy, standards, and infrastructure to enable secure delivery of online services.
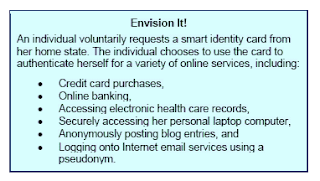
Lastly, the Strategy does not advocate for the establishment of a national identification card. Instead, the Strategy seeks to establish an ecosystem of interoperable identity service providers and relying parties where individuals have the choice of different credentials or a single credential for different types of online transactions. Individuals should have the choice of obtaining identity credentials from either public or private sector identity providers, and they should be able to use these credentials for transactions requiring different levels of assurance across different sectors (e.g., health care, financial, and social transactions).”
Of course they claim it will be “completely voluntary” but what happens when all of your favorite websites, including your bank require you to obtain a (not a national) identification card?
Jim Babka further writes,
“The “strategy” was unveiled practically on the eve of our 4th of July (ironic), and the deadline for public comment was set for July 19th. You were on holiday. Congress was out of session for half of the comment period as well. This strikes us as a deliberate attempt to avoid scrutiny.
After that deadline Congress will likely defer to the Department of Homeland Security, because of their supposed expertise, and the wheels of bureaucracy will begin to grind you into assimilation. Next stop, one Internet password for you, imposed and controlled by The State. Is this what you want?”
Me neither!